News
WhatsApp Privacy Scandal 2026: Lawsuit Claims Meta Can Read “Encrypted” Messages
Every time you open a WhatsApp chat, you are greeted by a comforting notification: “Messages and calls are end-to-end encrypted. No one outside of this chat, not even WhatsApp, can read or listen to them.”
For billions of users, this promise is the bedrock of trust. However, according to a bombshell lawsuit filed in January 2026 in a San Francisco federal court, that notification might be one of the most misleading statements in tech history.
International plaintiffs have dragged Meta to court, accusing the tech giant of deceiving the world. They allege that despite promises of total privacy, Meta has secretly built backdoors that allow it to store, analyze, and even view your private communications.
If you are worried about your security and want to know the truth behind these allegations, this article breaks down the legal battle that is shaking the foundations of secure messaging.
The Lawsuit: A Global Privacy Earthquake
The legal filing, which landed in late January 2026, represents a massive class-action effort. Plaintiffs from countries including Australia, Brazil, India, Mexico, and South Africa argue that Meta has systematically misled billions of users regarding the safety of their data.

This isn’t just a minor technical dispute; it is a direct challenge to WhatsApp‘s business model. The lawsuit claims that Meta creates a false sense of security to encourage users to share sensitive information, which the company then allegedly exploits for data analysis and ad targeting.
Key Details of the Filing:
- Court: San Francisco Federal Court (Northern District of California).
- Date: January 23, 2026.
- Accusation: Meta can bypass encryption keys to intercept messages.
- Status: Meta has vowed to fight the “frivolous” claims.
The Core Allegation: Is Encryption a Mirage?
The term “End-to-End Encryption” (E2EE) implies that a message is turned into a scrambled code on your phone and is only unscrambled on the receiver’s phone. In theory, this makes interception impossible.
However, the lawsuit argues that WhatsApp employs technical workarounds to bypass this protocol. The plaintiffs claim that Meta has implemented a “kleptographic backdoor.” This mechanism allegedly allows Meta engineers to create a “task” that grants them real-time access to a user’s chat history without the user ever knowing.
Note: The lawsuit cites unnamed whistleblowers—former content moderators—who claim they had “unfettered access” to supposedly secure messages to perform their jobs.
How the Alleged “Backdoor” Works
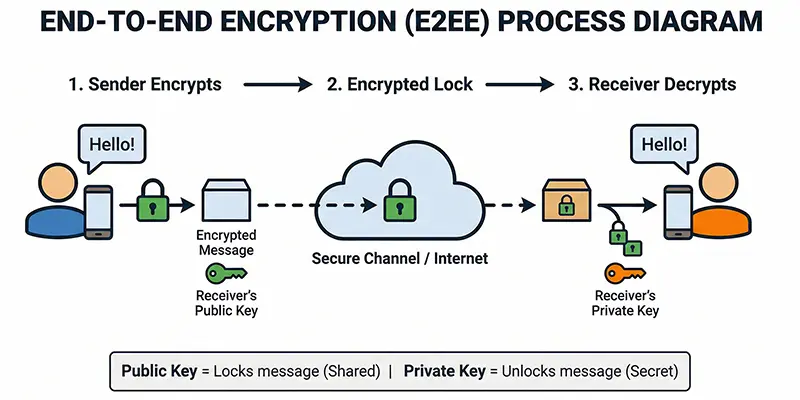
If the allegations are true, how is Meta doing it? The technical theory involves the way encryption keys are managed.
- Key Transparency: In a true secure environment, keys are generated only on user devices.
- The Bypass: The lawsuit suggests WhatsApp can force a “key change” or send a copy of the private key to Meta‘s servers.
- The Result: This would allow the company to decrypt WhatsApp messages on their side, effectively turning the app into a surveillance tool.
This level of vulnerability would mean that the “lock” on your digital door still works, but Meta secretly kept a master key.
Meta’s Defense: “False and Absurd”
Meta is not taking this lying down. The company issued a scorching denial immediately after the news broke. A Meta spokesperson labeled the lawsuit’s claims as “false and absurd,” threatening to pursue sanctions against the legal team filing the case.

The Signal Protocol Defense
Meta rests its entire defense on the Signal Protocol—widely considered the gold standard of cryptographic privacy.
- Official Statement: ” WhatsApp has been end-to-end encrypted using the Signal protocol for a decade. This means only the sender and recipient have the keys to unlock the messages. We cannot read them, even if we wanted to.”
- Technical Audit: Meta argues that independent security experts have audited the protocol and found no evidence of a universal backdoor.
Signal Protocol vs. Corporate Reality
Here is where the situation gets complicated. The Signal Protocol itself is open-source and secure. However, WhatsApp is a closed-source app.
This means that while the underlying math is solid, the app effectively runs inside a “black box.” Users cannot verify if Meta has added extra code on top of the protocol to siphon off data before it gets encrypted.
Security experts like Matthew Green from Johns Hopkins University have weighed in. While they express skepticism that a massive, undetected backdoor exists (as it would likely be spotted by network analysis), they acknowledge that metadata collection and “abuse reporting” tools do allow Meta to see some message content when a user flags a chat.
What This Means for Users in Pakistan and Globally
For users in Pakistan, where WhatsApp is the primary mode of communication for everything from business deals to family gossip, this news is alarming.
- High Usage: With millions of daily active users, Pakistan relies heavily on the platform.
- Data Sovereignty: If WhatsApp messages are accessible in San Francisco, it raises questions about international data sovereignty and who else might request access to this data.
- Trust Deficit: This lawsuit could trigger a migration to alternative apps if the plaintiffs provide concrete technical evidence.
Should You Switch to Signal?
If you are truly paranoid about your privacy, the lawsuit suggests you might want to switch to Signal (the app).

Unlike WhatsApp, Signal is:
- Non-Profit: It has no incentive to mine data for ads.
- Open Source: Anyone can inspect the code to ensure there are no backdoors.
- Minimalist: It collects virtually no metadata.
However, for most users, the “network effect” of WhatsApp—the fact that everyone you know uses it—makes switching difficult.
Conclusion: The Future of Your Messages
For now, this is a case of “He Said, She Said” with massive stakes.
If the plaintiffs can prove in court that Meta can technically view message content, it would mean the term “End-to-End Encryption” has been redefined to mean nothing. It would destroy trust in the platform instantly. But until proven otherwise, the math of encryption is usually stronger than the accusations of lawyers.
As we move through 2026, the outcome of this federal court case will determine the future of digital privacy. Until then, pay close attention to that little notification at the top of your chat—it might be the most controversial sentence on your phone.
Resources
- PC Magazine: Lawsuit Alleges That WhatsApp Has No End-to-End Encryption.
- Cryptography Engineering: WhatsApp Encryption, a Lawsuit, and a Lot of Noise.
- Computing UK: US probes claims Meta can access encrypted WhatsApp messages, report.
- Indian Express: The plaintiffs accuse Meta of violating the Federal Wiretap Act, a law that prohibits the intentional interception of electronic communications.
Frequently Asked Questions (FAQs)
According to a 2026 class-action lawsuit filed in San Francisco, WhatsApp’s claim of total privacy is being challenged. Plaintiffs allege that Meta has created a “backdoor” to bypass encryption keys, potentially allowing them to view message content. However, Meta denies this, stating they strictly use the secure Signal Protocol.
Officially, no. Meta states that only the sender and recipient have the keys to unlock messages. However, the new lawsuit alleges that technical workarounds exist that could allow Meta to intercept messages for data analysis and ad targeting, though this has not yet been proven in court.
The lawsuit accuses Meta of misleading billions of users about the security of their communications. Filed in federal court, it claims that while WhatsApp advertises “End-to-End Encryption,” the company actually retains the ability to decrypt and analyze private messages via a hidden backdoor.
If you are highly concerned about privacy, security experts often recommend Signal. Unlike WhatsApp, Signal is open-source (meaning its code can be inspected by anyone), is a non-profit organization, and collects virtually no metadata on its users.
With millions of users in Pakistan relying on WhatsApp for business and personal use, this lawsuit raises serious concerns about data sovereignty. If a backdoor exists, it could potentially be exploited not just by Meta for ads, but by third parties or governments for surveillance.
Related Blogs
Meta Premium Subscription Alert: New Paywall Hits Facebook, Instagram & WhatsApp (2026)
Meta is rolling out a new Meta Premium Subscription in 2026. Unlock Instagram Anonymous Story Viewer, Meta AI tools, and WhatsApp Business upgrades. See what is behind the paywall.
Feb
WhatsApp Premium Pakistan: The Shocking €4 Ad-Free Subscription Truth (2026)
Is WhatsApp Premium coming to Pakistan? Discover the truth about the new €4 ad-free subscription, the "Pay or Consent" model, and why Pakistani users might be stuck with ads in 2026.
Feb
Clawdbot (Moltbot) Explained: The ‘Claude AI’ Agent Taking Control of WhatsApp
Discover Clawdbot (Moltbot), the new open source Claude AI agent that connects to WhatsApp. Learn about its root access, automation capabilities, and the security risks involved.
Jan